[ad_1]
In a nutshell: USB worms are traditionally designed to spread wherever they can, hopping on any removable storage device they can find. When cyber-espionage and cyber-war enter the fray, this spreading capability can work against the malware’s original intent.
Check Point Research recently discovered and analyzed a new worm with USB spreading capabilities, a seemingly “simpler” malware created by Gamaredon, a well-known group working with the Russian Federal Security Service (FSB). Also known as Primitive Bear, ACTINIUM, and Shuckworm, Gamerdon is an unusual player within the Russian espionage ecosystem, which aims almost exclusively at compromising Ukraine targets.
Check Point said that while other Russian cyber-espionage teams prefer to hide their presence as much as they can, Gamaredon is known for its large-scale campaigns while still focusing on regional targets. LitterDrifter, the group’s recently discovered worm, seems to adhere to Gamaredon’s usual behavior as it has likely gone way beyond its original targets.
LitterDrifter is a worm written in the much-maligned VBScript language (VBS) with two main functionalities: “automatic” spreading over USB flash drives, and listening to remote orders coming from the creators’ command&control (C2) servers. The malware seems to be an evolution of Gamaredon’s previous efforts with USB propagation, Check Point researchers explained.
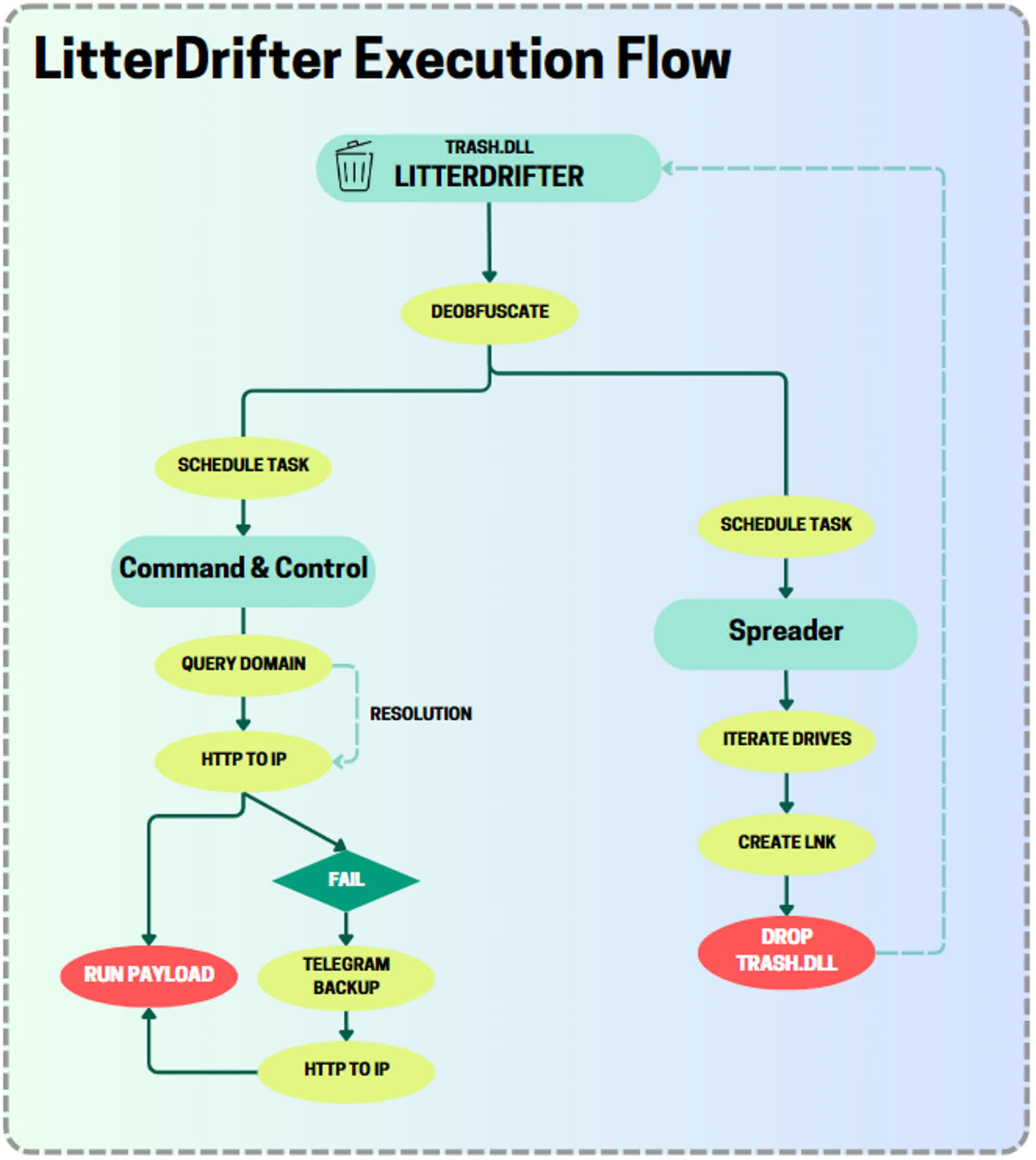
LitterDrifter employs two separate modules to achieve its goals, which are executed by a “heavily obfuscated” orchestrator VBS component found in the trash.dll library. The worm tries to establish persistence on Windows systems by adding new scheduled tasks and Registry keys, exploiting the Windows Management Instrumentation (WMI) framework to identify USB targets and create shortcuts with random names.
The worm tries to infect a USB target as soon as the flash drive is connected to the system. After infection, LitterDrifter tries to contact a C2 server hidden behind a network of dynamic IP addresses which usually last as long as 28 hours. Once a connection has been established, LitterDrifter can download additional payloads, decode and finally execute them on a compromised system.
Check Point Research said that no further payloads were downloaded during the analysis job, which means that LitterDrifter is likely the first stage of a more complex, ongoing attack. The majority of LitterDrifter infections were discovered in Ukraine, but the worm was also identified on PCs located in the US, Germany, Vietnam, Chile, Poland. Gamaredon has likely lost control of its worm, which ultimately spread to unintended targets before the full attack was deployed.
[ad_2]
Source link