[ad_1]
As a TechSpot reader you’ve surely opened software as an admin on Windows before — maybe as recently as today — so the function probably isn’t foreign to you. However, we were curious to know more about what happens under the hood of Windows when you tell the operating system to run a program as an administrator, and why this process is necessary in the first place.
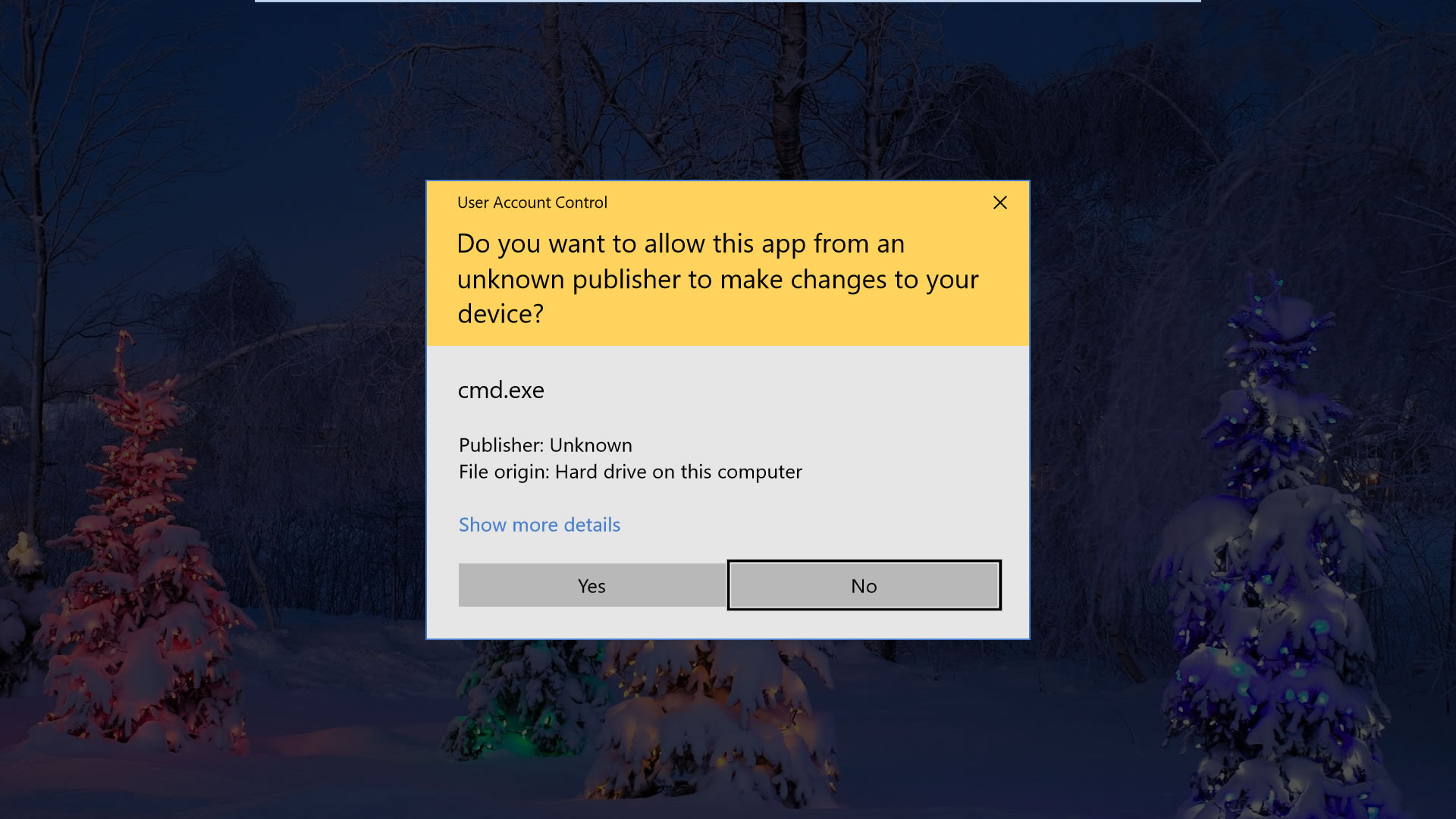
Those of you who made the transition from XP to Vista will probably remember the introduction of “User Access Control” (UAC) or “Mandatory Integrity Control” (MIC). The security feature, which remains part of Microsoft’s OS, prompts you when software tries making changes to your system and rests at crux of why applications sometimes require “elevated” access.
When you log in to Windows, your account is assigned a token that contains identifying information including your user groups and privileges such as read, write, and execute permissions.
Among the information in that token is an integrity level which is used by the operating system determine the trustworthiness of objects like files, registry keys for the purpose of informing users when installations are being launched as well as isolating processes from having unnecessary access to system files.
Editor’s Note: This feature was originally published on October 8, 2018. It’s just as relevant and current today as it was then, so we’ve bumped it as part of our #ThrowbackThursday initiative.
The Windows Mandatory Integrity Control (MIC) mechanism has at least six different integrity levels: untrusted, low, medium, high, system and trusted installer.
By default, a standard user account has a medium integrity, which is the maximum level available for a process to be created when you open an executable file without providing elevated access via admin credentials.
When you right-click on a file or program and choose “Run as administrator,” that process (and only that process) is started with an administrator token, thus providing high integrity clearance for features that may require the additional access to your Windows files etc.
The different Windows integrity levels:
- Untrusted Integrity: Given to anonymous processes.
- Low Integrity: Commonly used for Web-facing software such as browsers.
- Medium Integrity: Applied to standard users and used for most objects.
- High Integrity: Administrator-level access, generally requires elevation.
- System Integrity: Reserved for the Windows kernel and core services.
- Trusted Installer: Used for Windows Updates and system components.
Processes started by opening an exe from a Windows account with medium clearance will have that integrity level unless the executable file is set to low, and developers are encouraged to use the lowest access possible, ideally avoiding instances where software will require high integrity to thwart unauthorized code (malware) from taking root.
The practice of “least-privilege” design is applied to Windows’ own administrator accounts, which receive both standard and admin-level tokens upon logging in, using standard/medium integrity access when possible instead of high.
Although Microsoft recommends against running programs as an administrator and giving them high integrity access without a good reason, new data must be written to Program Files for an application to be installed which will always require admin access with UAC enabled, while software such as AutoHotkey scripts will often need elevated status to function properly.
Here are all the ways we could find to open executable files with administrator access (high integrity) on Windows 10, including some methods that will configure software to always open with elevated access:
Ways to run a program as an administrator on Windows
Starting with the most obvious: you can launch a program as an administrator by right-clicking on the executable file and choosing “Run as administrator.”
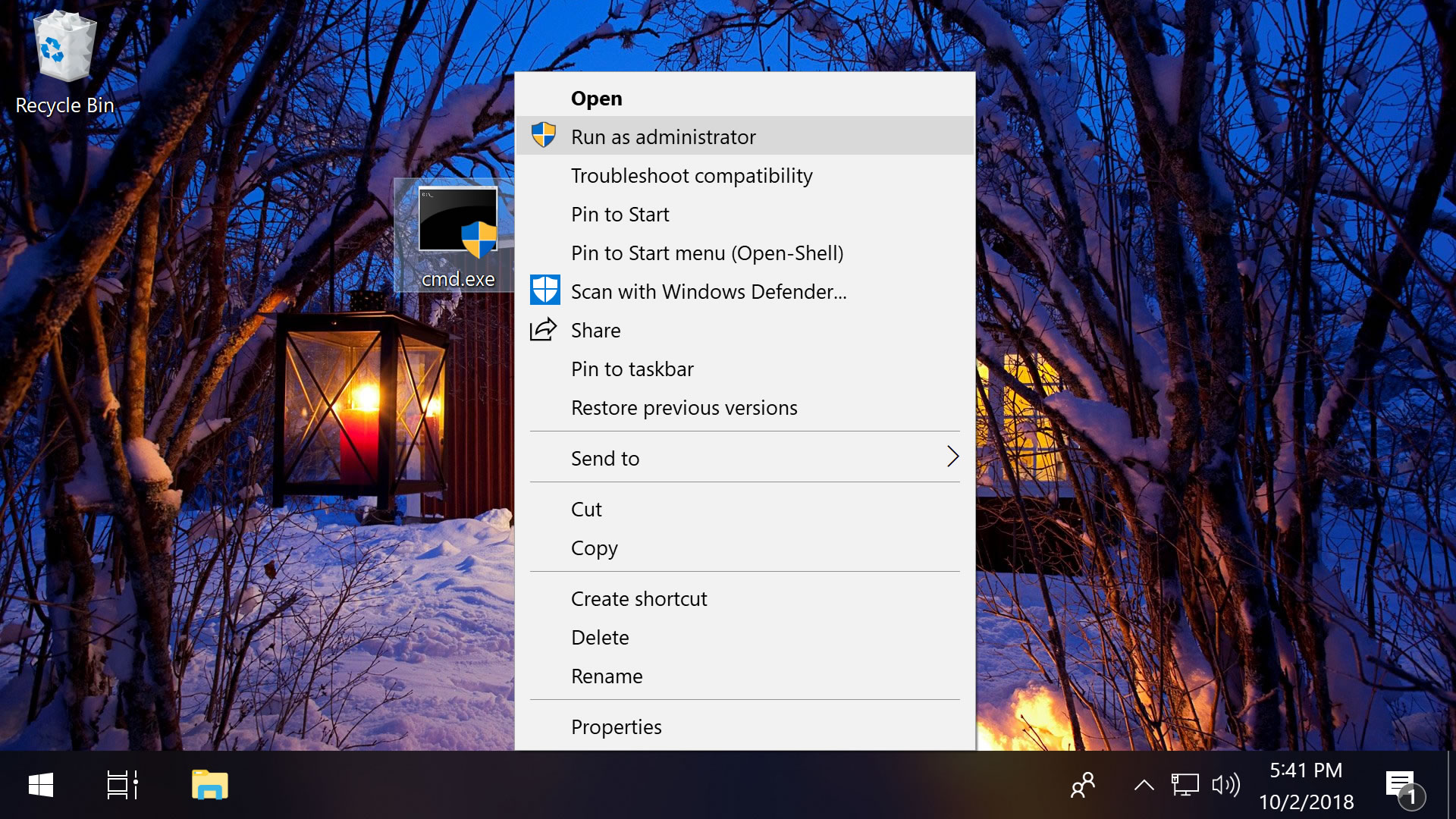
As a shortcut, holding Shift + Ctrl while double-clicking the file will also start the program as an admin.
Separately, holding only Shift while you right-click on the file will add “Run as a different user…” to the context menu, which opens a screen where you can enter another user’s credentials, including the administrator account (the username is Administrator and may not have a password if you haven’t applied one).
These locations also have shortcuts to admin access…
Start Menu: Right-click an executable like anywhere else for the option to launch a program as an administrator.
Taskbar: Click a program on your taskbar to open the jump list, then right-click the exe from that menu for the admin option.
File Explorer: Select the file in File Explorer > Click Manage in the Ribbon menu up top > Choose “Run as administrator.”
Run prompt: Enter this line into Run (Windows key + R): RunAs.exe /user:Administrator “cmd.exe“
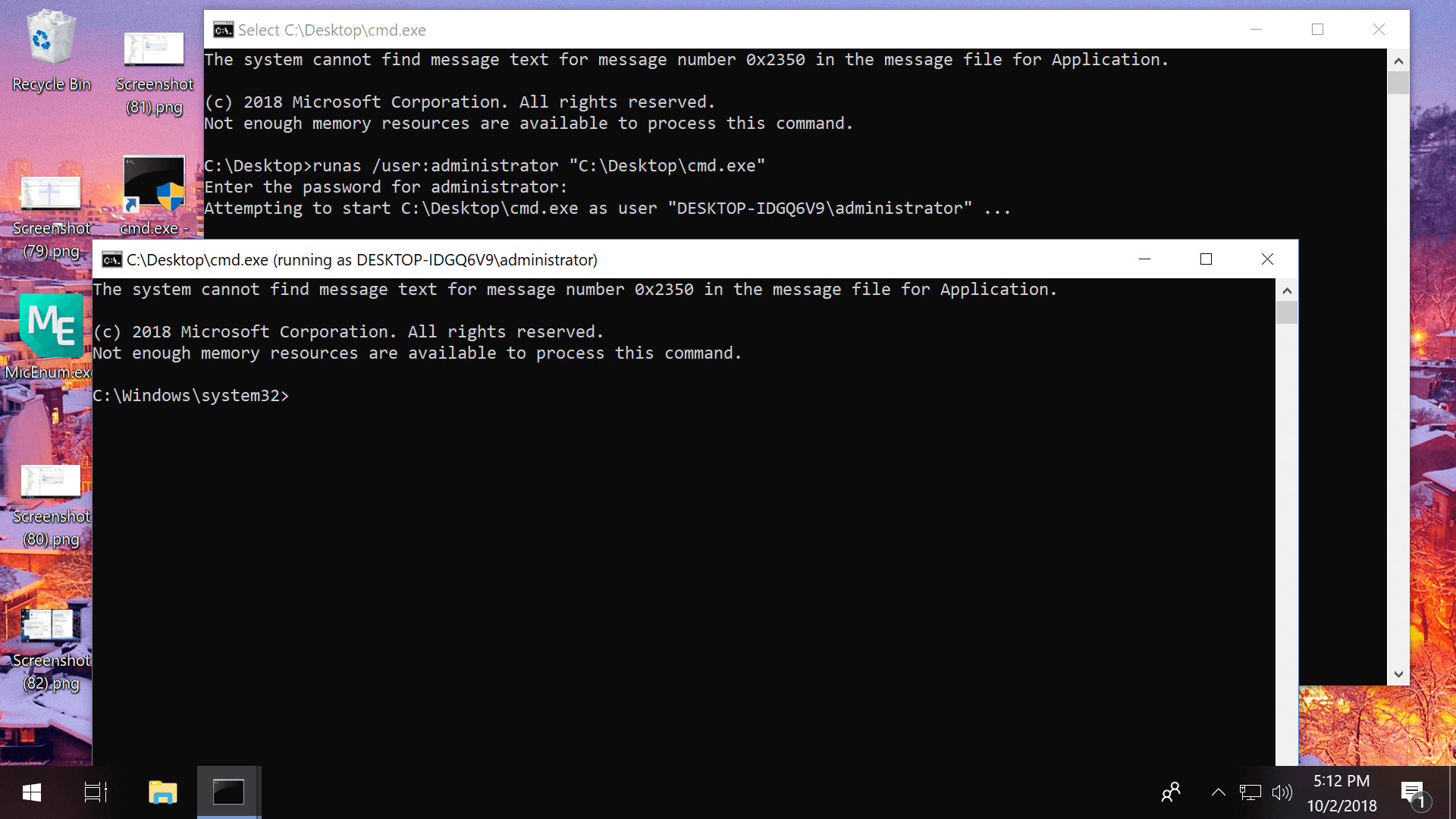
Command Prompt: From the command line, enter this with your file location: runas /user:administrator “C:UsersTechSpotDesktopfile.exe“
Task Manager: Click File > Run new task > Check the box next to “Create this task with administrative privileges” > Enter the location of your file (example: C:UsersTechSpotDesktopfile.exe)
Task Scheduler: When creating a new task (Action > Create Task), enable these settings in the “General” tab: “Run whether user is logged on or not” and “Run with highest privileges”
Note that the Command Prompt method didn’t work until we enabled the Administrator account and changed another setting that would allow the command to be entered without a password:
- Search Start or Run for compmgmt.msc > Go to Local Users and Groups > Users > double-click on Administrator and uncheck “Account is disabled”
- Search Start or Run for gpedit.msc > Go to Computer Configuration > Windows Settings > Local Policies > Security Options > Double-click the option Accounts: Limit local account use of blank passwords to console logon online and choose Disable
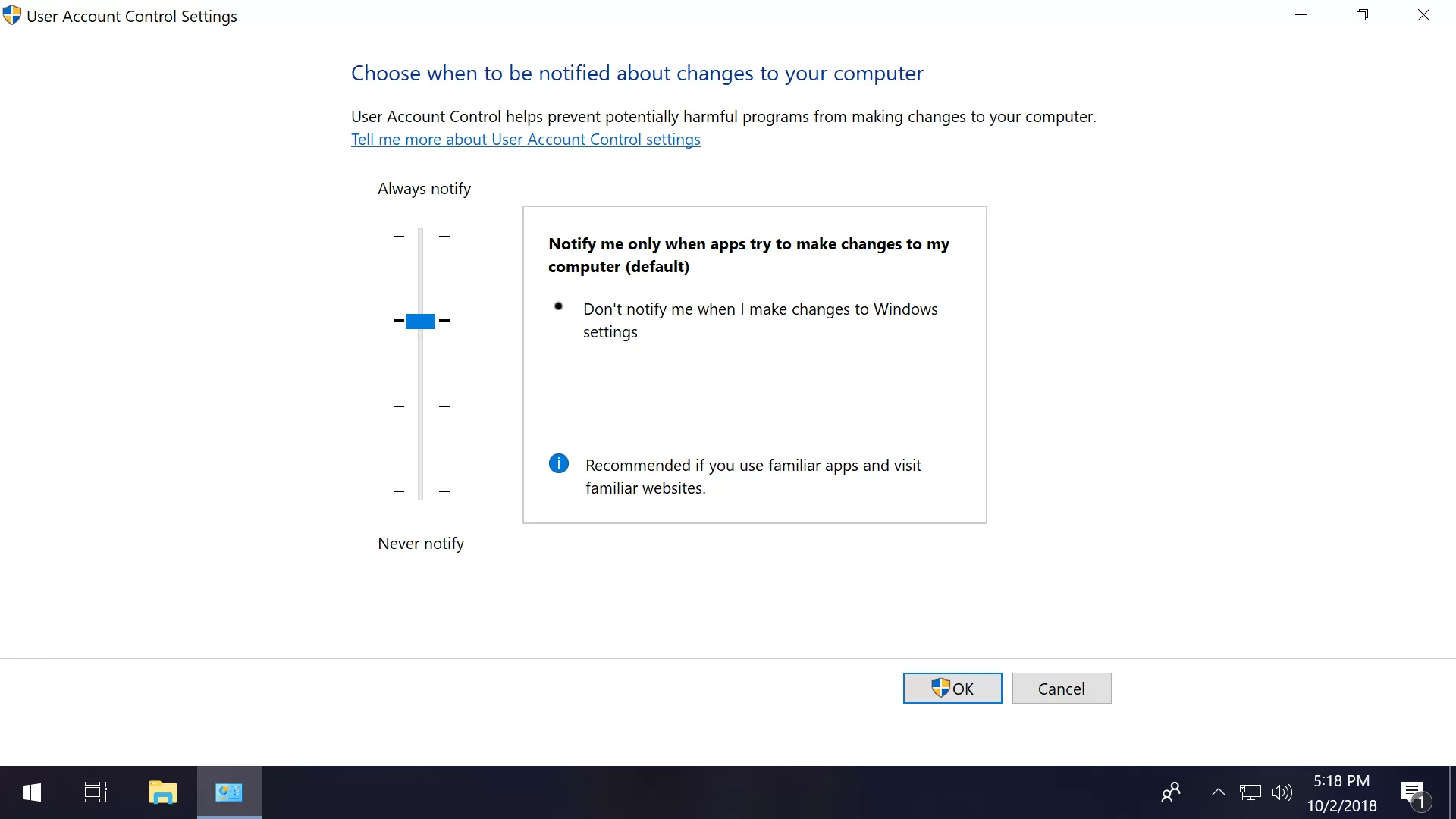
Also, in the same section of the Group Policy Editor (gpedit.msc) that we just mentioned are a range of options to fine-tune Windows’ User Account Control settings (scroll all the way down).
How to set programs so they always start as an admin
Given Microsoft’s philosophy of providing programs with the least amount of access possible, configuring an application to always run as an administrator is generally not recommended but sometimes convenient when the software always requires elevation so you don’t have to jump through those hoops every time. Here are a few ways to accomplish that:
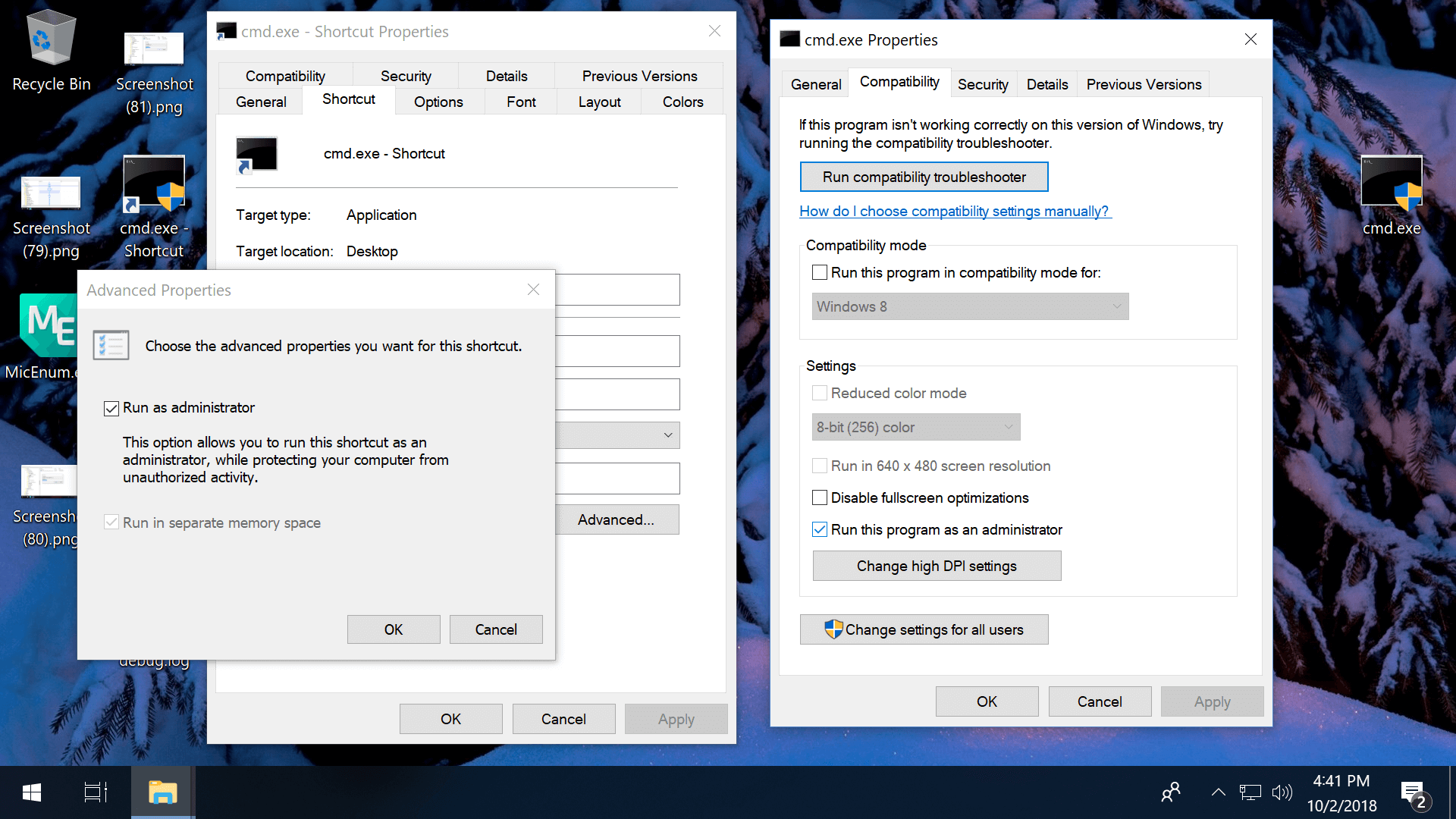
Always run as admin from a shortcut: Right-click on a shortcut file > Shortcut tab > Advanced > Check the box to “Run as administrator”
Note that you can create a shortcut file by right-clicking the main exe, and that if you copy the shortcut into C:UsersTechSpotAppDataRoamingMicrosoftWindowsStart MenuProgramsStartup the program will automatically start with Windows as you sign in.
Always run as admin via Compatibility Properties: Right-click on an exe > Properties > Compatibility tab > Check the box to “Run this program as an administrator.”
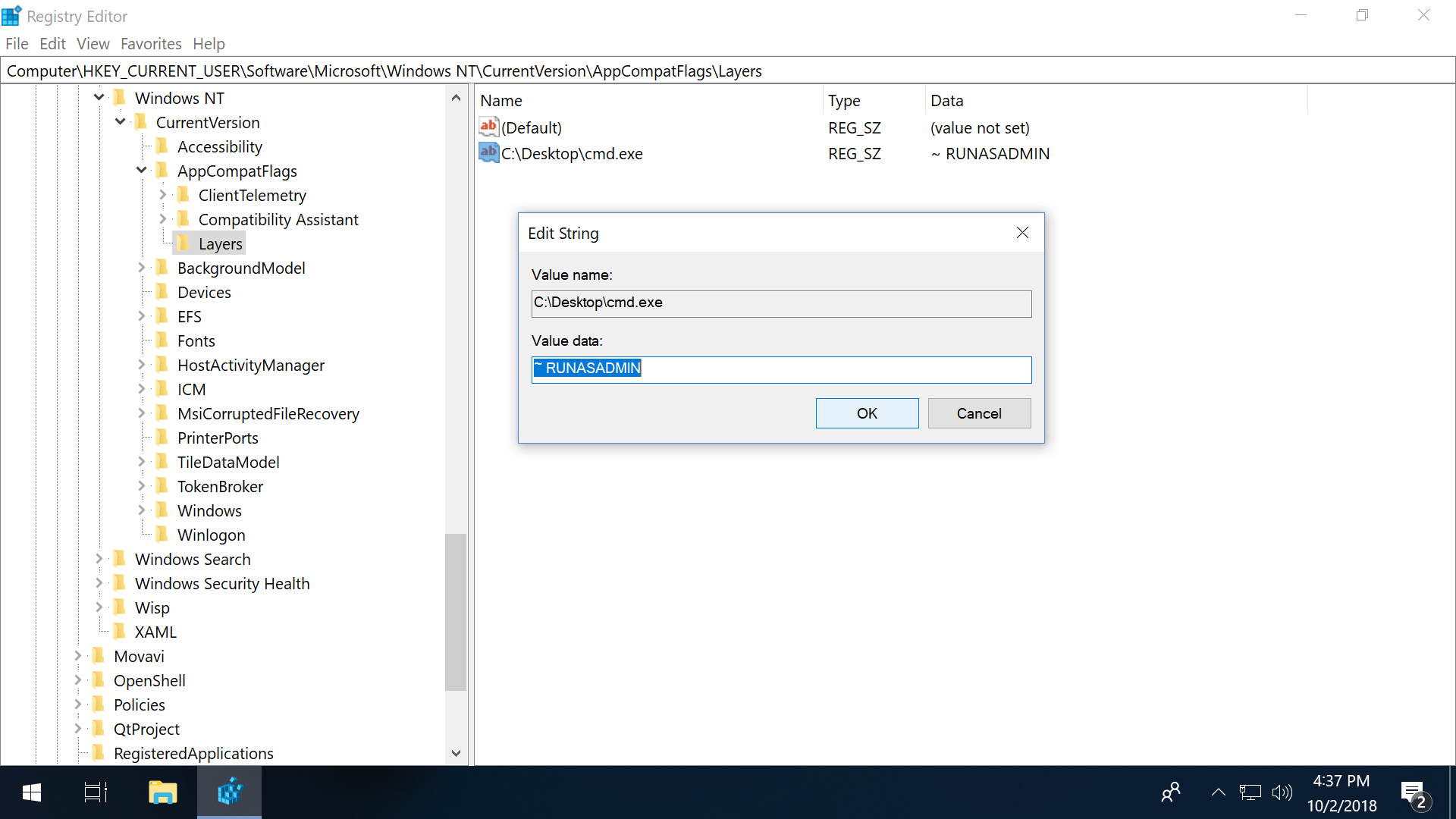
Always run as admin via the Registry Editor:
- Navigate to: HKEY_CURRENT_USERSoftwareMicrosoftWindows NTCurrentVersionAppCompatFlagsLayers
- If “Layers” is missing, right-click AppCompatFlags and add a new key named Layers
- Right-click Layers (either the folder or in the right pane) an create a new String Value
- Set the value name as the full path of the exe file
- Set value data as ~ RUNASADMIN
Bonus
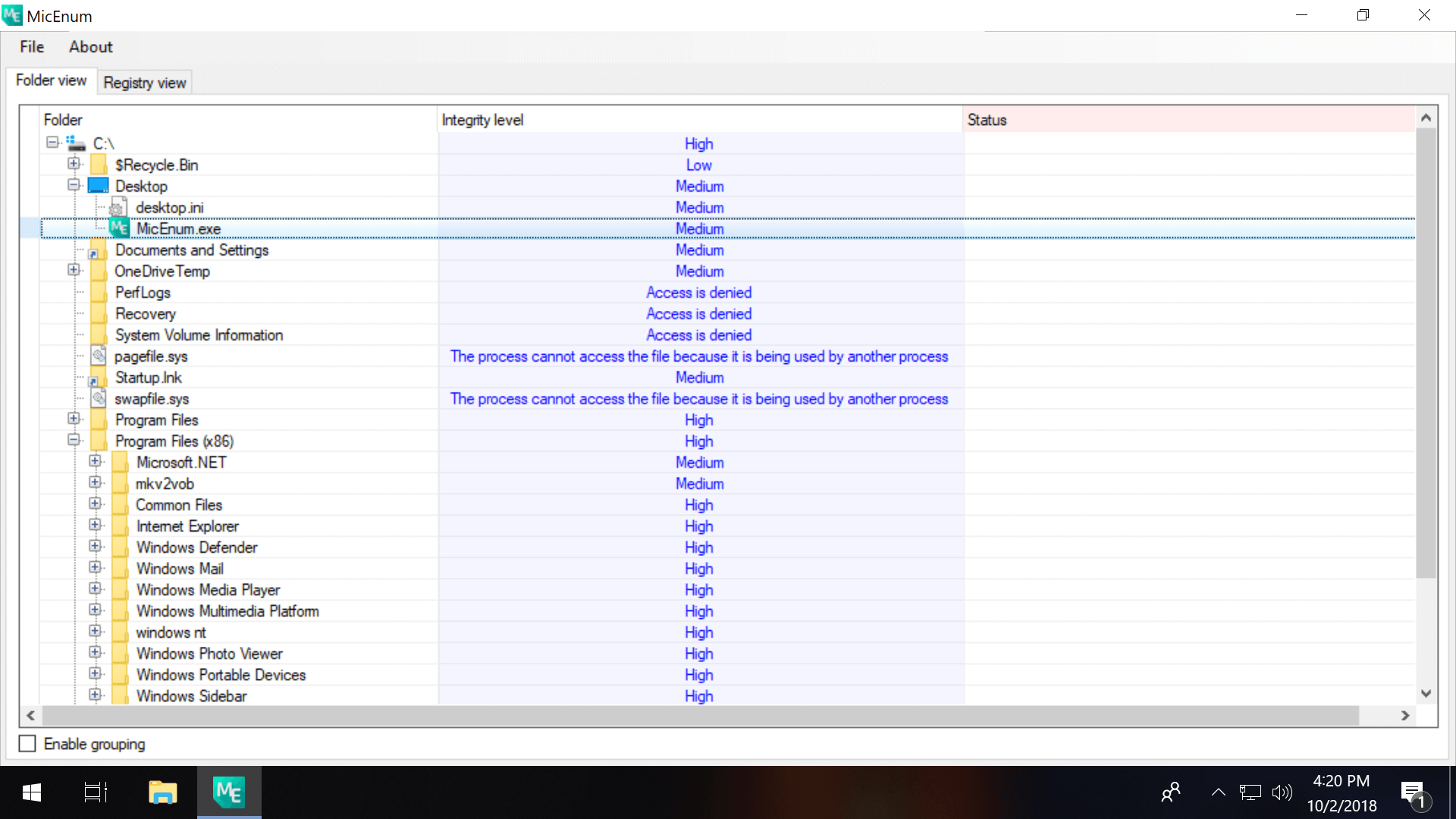
#1 Third-party software including MicEnum will generate a list of Windows files/folders and their integrity levels, including the ability to set a new integrity level as well as browse in both folder and registry views.
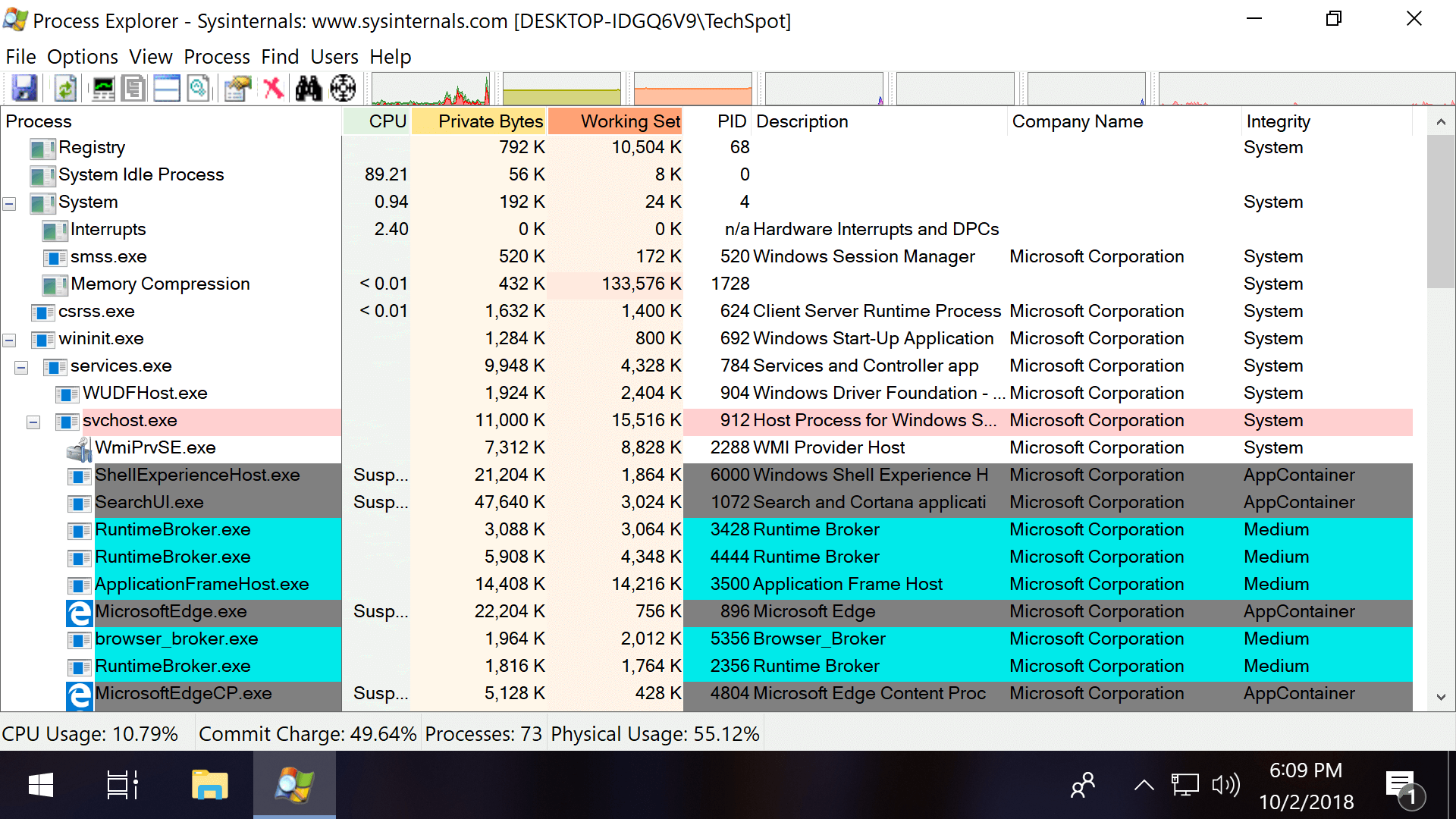
Process Explorer (pictured in the intro of this article) also has the ability to display integrity levels if you right click the horizontal bar with CPU, Private Bytes etc. and open the properties (check the box next to Integrity Levels).
#2 On a new Windows installation, the first user account created is a local administrator account while subsequent accounts are standard users. By default, the built-in administrator account is disabled. You can enable the account so it’s available when you log in to Windows by entering this line into Command Prompt (use “no” to disable it again): net user administrator /active:yes
#3 Microsoft has different utilities such as Elevation PowerToys and PsExec which can also be used to gain administrator access but span beyond the scope of this guide.
More Useful Tips
[ad_2]
Source link

